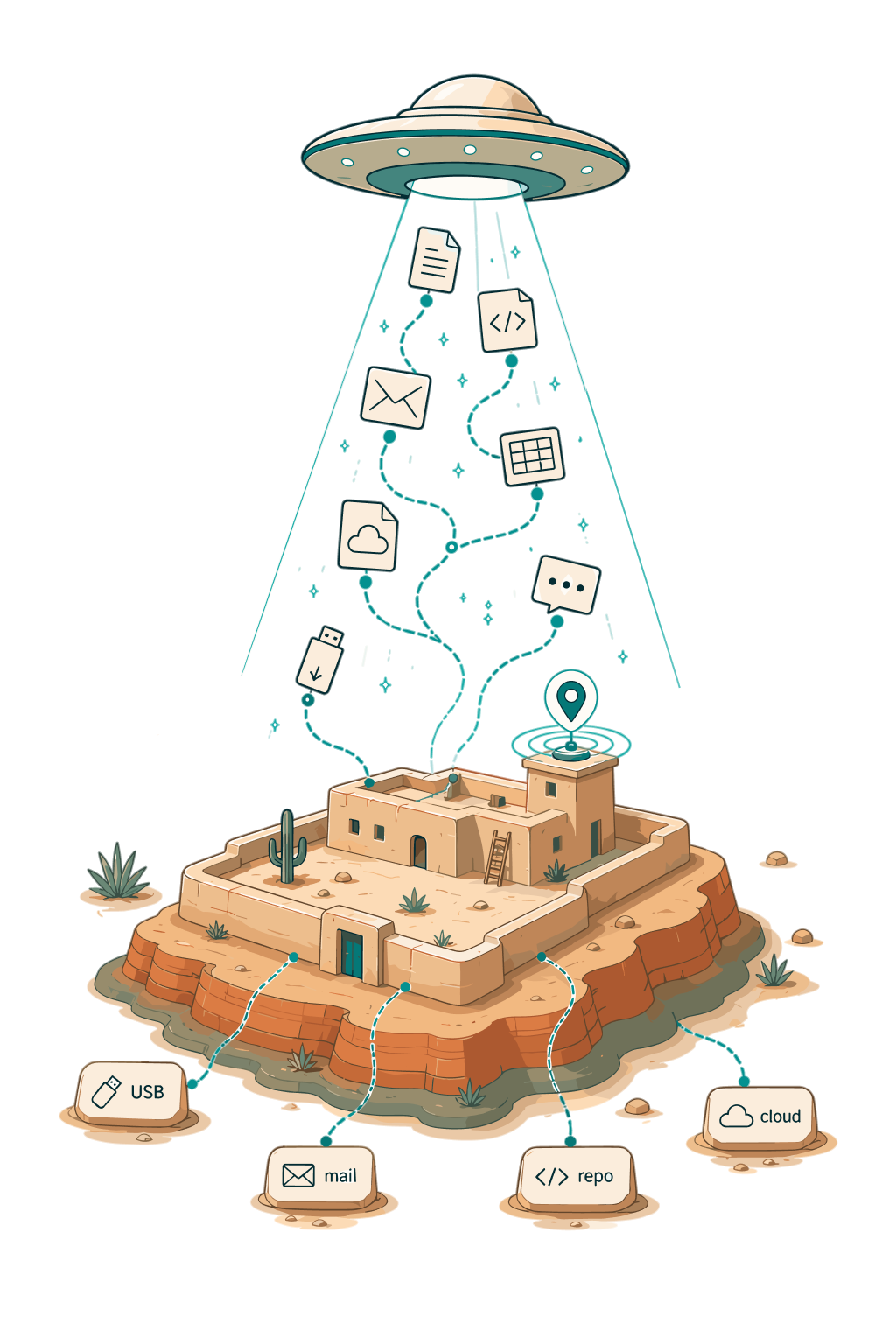
When information leaves, find it fast.
Reconstruct what an employee touched, copied, or transmitted across endpoints, cloud, and chat — with citations back to artifacts and a clear path to verify every finding.
Move at the speed of the incident
Build a defensible timeline across phones, laptops, mailboxes, and cloud accounts in hours, not weeks.
See exfiltration the parser missed
Cross-reference notification logs against message stores. Surface deletions, side accounts, and channel-hopping that single-tool reviews never catch.
Give counsel something they can use
Every finding ships with the source artifact and the steps to verify it in Physical Analyzer, AXIOM, or the native tool.
How Mobasi handles departures and exfiltration
Build a timeline
Hand Mobasi a phone, laptop, and mailbox. Get a one-page map of what they touched, who they spoke to, and what walked out the door.
Reconstruct communications
Correlate iMessage, Signal, WhatsApp, and Slack into a single timeline so you can see when conversations moved off-channel.
Analyze the movement of data
Cross-reference USB mounts, cloud sync activity, and external sharing signals to surface large-volume staging events.
Pivot to any account
Pull personal Gmail, ProtonMail, and burner accounts into the same investigation as O365 and Workspace.
Analyze gaps in evidence
Flag what is missing from the message store — deleted threads, cleared caches, wiped volumes — and tell you when it happened.
Prepare a counsel-ready report
Export a verification-first report with hashes, timestamps, and the exact command to reproduce each finding.
Enterprise-grade security
Bring it to your case.
See how Mobasi works on your evidence and workflow.